Institutional custody reporting ensures the secure management of digital assets, particularly cryptocurrencies, by focusing on transparency, security, and compliance. With cryptocurrency losses exceeding $6.5 billion in 2024, robust custody practices are critical to protecting assets and maintaining trust. Key practices include:
- Transparency: Real-time visibility, independent audits (e.g., SOC 2 Type II), and asset segregation to ensure client funds are separate from custodians’ operational funds.
- Security: Layered safeguards like cold storage, Multi-Party Computation (MPC), and insurance coverage for theft and fraud.
- Regulatory Compliance: Adherence to standards set by the SEC and NYDFS, including the use of qualified custodians and written disclosures.
Custody reporting has evolved into a critical tool for mitigating risks, meeting fiduciary obligations, and navigating the growing digital asset landscape. Institutions must prioritize clear reporting, independent verification, and advanced technology to ensure asset protection and compliance.
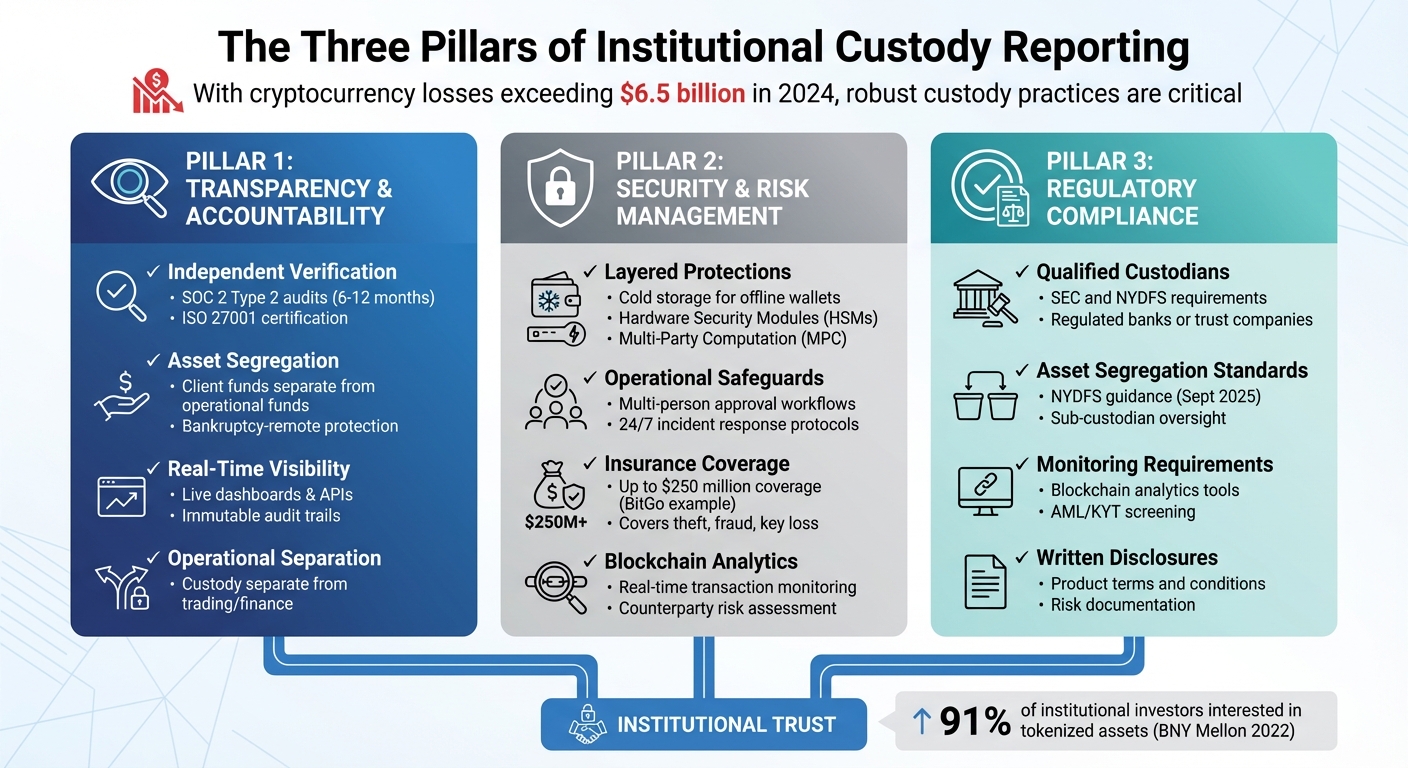
Three Pillars of Institutional Custody Reporting: Transparency, Security, and Compliance
How Top Institutions Manage Risk, Custody & Compliance in Crypto | UK & Global Perspectives
sbb-itb-7e716c2
Core Principles of Custody Reporting
These principles form the backbone of a custody reporting system designed to protect digital assets. Institutions aiming to manage these assets responsibly must focus on institutional digital asset services across three key areas: transparency and accountability, security and risk management, and regulatory compliance.
Transparency and Accountability
Transparency starts with independent verification. Certifications like SOC 2 Type 2 and ISO 27001, once optional, became essential by 2026. SOC 2 Type 2 audits evaluate how effective security controls are over a period of 6–12 months, offering stakeholders evidence that these measures work consistently.
Another cornerstone of accountability is asset segregation. Client assets must be kept legally and physically separate from a custodian’s operational funds to ensure they are protected, even in cases of bankruptcy. Past failures in the industry, often tied to the mixing of client and operational funds, highlight the importance of custodial agreements that specify assets are held in trust or separate legal entities – not on a custodian’s balance sheet.
The demand for real-time visibility has replaced outdated periodic snapshots. Today, institutions expect constant access to holdings through dashboards and APIs that integrate with internal risk systems. Immutable audit trails document every transaction and access attempt, creating records that are crucial for both internal governance and regulatory checks. Additionally, separating custody operations from trading or finance functions ensures that no single team has control over both asset access and transaction approvals, reducing the risk of internal fraud.
"In the volatile world of digital assets, trust is the ultimate currency. Compliance certifications like SOC 2 and ISO 27001 are not just checkboxes; they are foundational pillars of that trust for institutional investors." – Sahaza Marline R., CryptoCursor
While transparency builds trust, strong security measures are equally critical to minimize risks.
Security and Risk Management
Security reporting must demonstrate layered protections that eliminate single points of failure. This includes using cold storage for offline wallets, Hardware Security Modules (HSMs) for active keys, and Multi-Party Computation (MPC) to divide private keys into encrypted shares. MPC has become the industry standard, replacing traditional single-key systems that are more vulnerable to theft or loss.
Operational risks should be documented with evidence of safeguards such as multi-person approval workflows for large transfers and 24/7 incident response protocols. For instance, in October 2022, BNY Mellon introduced its digital asset custody platform for Bitcoin and Ether. The platform integrated Fireblocks’ security technology and Chainalysis’ compliance analytics, setting a benchmark for institutional-grade risk management. Blockchain analytics tools like these enable real-time monitoring of transactions to flag suspicious activity and assess counterparty risks.
Insurance coverage is another critical factor. Custodians must clearly disclose coverage limits and exclusions so stakeholders know what is protected. For example, BitGo offers up to $250 million in insurance for digital assets, covering theft, internal fraud, and private key loss. Reporting frameworks should detail the scope of this insurance, including specific limitations.
Security measures alone, however, are not enough. Adhering to regulatory standards is equally important.
Regulatory Compliance
In the U.S., regulators have defined custody standards to protect digital assets. The SEC and the New York Department of Financial Services (NYDFS) require registered investment advisers to use "qualified custodians" – regulated banks or trust companies that can independently verify their safekeeping practices. On September 30, 2025, the NYDFS updated its guidance for virtual currency custodians, emphasizing strict asset segregation and requiring sub-custodians to operate under comparable regulatory frameworks.
The SEC’s Division of Investment Management also issued a no-action letter, allowing RIAs and Regulated Funds to treat state trust companies as qualified custodians, provided they meet specific cybersecurity and financial reporting criteria. These steps signal a shift toward clearer, enforceable rules rather than ad-hoc enforcement actions.
Custodians using omnibus accounts must maintain internal systems that clearly identify each customer’s beneficial interest. Additionally, blockchain analytics tools are now expected to monitor fund sources and detect suspicious activity. Written disclosures outlining product terms, conditions, and risks are also mandatory, ensuring clients fully understand what they’re agreeing to.
Key Elements of Effective Custody Reports
Institutional clients require clear evidence that their assets are secure, that safeguards are functioning as intended, and that custodians operate efficiently. These reports must address both regulatory standards and client expectations, focusing on critical elements.
Asset Segregation and Verification
Ensuring assets are segregated is a key defense against fraud and insolvency risks. Custody reports need to confirm that client assets are stored in distinct accounts or wallets, separate from the custodian’s operational funds. This legal separation ensures that even in cases of financial collapse, client assets remain protected.
Take Prime Trust’s 2023 collapse as an example: an $82 million shortfall caused by commingled funds highlighted the risks of poor segregation practices. Reports should document trust structures or custodial agreements that explicitly designate assets as customer property, not liabilities on the custodian’s balance sheet.
Additionally, independent verification is essential. This includes confirming asset authorization, custody, and accurate recordkeeping. Tools like on-chain audit trails and real-time dashboards provide unalterable proof of asset ownership and movement, replacing reliance on trust with verifiable data. Multi-person approval workflows, such as multi-signature schemes or "four-eyes" reviews, further prevent unauthorized transfers by ensuring no single individual has unchecked control.
Audit and Certification Documentation
Segregation efforts are only as strong as the operational integrity behind them. Third-party audits validate that custodians maintain and execute their security measures effectively. In North America, SOC 2 Type 2 reports are the benchmark, as they assess security controls over a 6-to-12-month period rather than a single point in time. This distinction is critical: while SOC 1 Type 1 reports confirm controls on a specific date, SOC 2 Type 2 reports demonstrate consistent performance.
For instance, BitGo holds both SOC 1 Type II and SOC 2 Type II certifications, showcasing the reliability of its security and financial systems. These certifications are integral to their compliance framework for qualified custody solutions. Additionally, ISO 27001 certification offers a globally recognized framework for managing information security risks, essential for custodians working with international clients.
Comprehensive custody reports should include these audit documents or at least attestation letters from independent auditors. Institutions must also confirm that the audit scope covers the specific custody and key management services they use, rather than just general IT operations.
Performance Metrics and Benchmarks
Segregation and audits form the foundation, but ongoing performance tracking ensures custodial reliability. Operational metrics, such as real-time dashboards, can provide insights into account balances, withdrawal logs, and access histories. These should be paired with documented Service Level Agreements (SLAs) and incident resolution timelines. Together, these metrics allow institutions to evaluate whether custodians meet standards for uptime, transaction speed, and response times.
Consider the February 2025 Bybit breach, where a $1.4 billion loss occurred due to a wallet infrastructure exploit. The attack relied on sophisticated social engineering to trick three authorized approvers. However, institutional managers using Forteus’s multi-manager product mitigated further risk by withdrawing most assets within an hour of the breach. This underscores the importance of rapid incident response protocols and effective monitoring.
Custody reports should also include compliance and risk metrics, such as Know-Your-Transaction (KYT) scores and blacklisted wallet filtering. These demonstrate adherence to anti-money laundering (AML) and counter-terrorist financing (CTF) standards. With cryptocurrency losses reported to the FBI exceeding $6.5 billion in 2024, such metrics are vital evidence of active risk management. When combined with audits and strict segregation, these elements ensure transparency and security in institutional custody reporting.
| Report Component | Essential Data Points | Compliance/Transparency Goal |
|---|---|---|
| Asset Verification | On-chain audit trails, wallet addresses | Proof of Reserve and Segregation |
| Security Audits | SOC 2 Type 2, ISO 27001, Penetration tests | Operational Integrity |
| Performance Metrics | SLA compliance, incident resolution speed | Custodian Effectiveness |
| Regulatory Data | KYT scores, AML/KYC status, Tax reporting | Legal Compliance |
Best Practices for Institutional Custody Reporting
Institutional custody reporting thrives on three pillars: transparency, security, and regulatory compliance. By following these practices, institutions can ensure their custody operations are both reliable and trustworthy.
Regular Reporting Cadence
A consistent reporting schedule is key to building trust and ensuring transparency. Institutions should align their internal reporting processes with the requirements of regulatory bodies like the SEC, MiCA, and DFS. Modern custody systems now offer real-time visibility through dashboards and APIs, enabling institutions to instantly access details like holdings, balances, and access logs. Automating data collection through integrated APIs not only minimizes manual errors but also provides audit-ready reports on demand.
Regular third-party evaluations are another critical element. Conducting SOC 1 and SOC 2 Type II audits – typically covering a period of 6–12 months – provides independent verification of controls, which is essential for maintaining stakeholder confidence. Additionally, institutions can enhance their reporting practices by using blockchain analytics tools for continuous monitoring of transactions. These tools help maintain immutable audit trails for all workflows, including authorization and access changes.
Using Technology for Reporting
Once a structured reporting schedule is in place, leveraging technology can take reporting accuracy and efficiency to the next level. API integration plays a pivotal role, creating seamless data flows between custody platforms and institutional systems. This reduces the need for manual data entry, which has historically been a source of reconciliation errors.
"Custodians should provide detailed reporting APIs and dashboards, so that institutions can get real-time visibility into their holdings and satisfy their own auditors and regulators."
– Integral
Built-in compliance tools further streamline the process by automating AML and KYT screenings. These tools integrate regulatory requirements directly into the custody environment, using features like smart contract-based transfer restrictions and real-time risk scoring.
Independent Audits and Oversight
Automated reporting is powerful, but it must be complemented by independent audits to provide unbiased validation of custody controls. SOC 2 Type II audits are particularly valuable because they assess whether a custodian’s controls function effectively over time, unlike Type I audits, which only confirm the existence of these controls.
Independent audits also serve as a safeguard against internal risks, such as the mismanagement of client funds. A cautionary example is the collapse of Prime Trust in 2023, which resulted in an $82 million shortfall due to fund commingling. With cryptocurrency-related losses reported to the FBI exceeding $6.5 billion in 2024, third-party oversight is more critical than ever. Institutions should ensure their custodians enforce bankruptcy-remote policies through clear legal agreements and carefully vet any sub-custodians responsible for safeguarding assets.
BeyondOTC‘s Role in Institutional Custody Reporting
BeyondOTC builds on established custody reporting practices to meet the additional demands of institutional clients. Handling large-scale cryptocurrency transactions comes with unique challenges, especially when institutions must maintain strict transparency and security standards. BeyondOTC addresses these challenges by connecting institutions with specialized service providers essential for compliant custody operations.
Facilitating Secure OTC Transactions
BeyondOTC provides OTC trading solutions tailored for high-value transactions, helping institutions avoid risks like slippage and market exposure commonly associated with public exchanges. To date, the platform has facilitated over $250 million in Bitcoin transactions and more than $30 million in OTC altcoin deals, showcasing its ability to manage institutional-scale volumes. BeyondOTC also offers tools like advanced analytics, secure data sharing, and instant notifications, ensuring audit-ready reporting. With 24/7 trading support and a network spanning over 50 countries, the platform ensures smooth international settlements. This streamlined approach supports both regulatory compliance and strategic industry connections.
Regulatory Compliance Consulting
BeyondOTC provides legal consultancy services to help clients implement strong regulatory frameworks. By connecting institutions with top legal firms specializing in blockchain and cryptocurrency law, BeyondOTC ensures clients meet all necessary compliance requirements. This guidance directly supports the secure and transparent reporting practices institutions rely on.
Networking with Key Industry Players
Through its extensive network, BeyondOTC links institutional clients with trusted custodians, including state-chartered trust companies and regulated banks. These custodians hold certifications like SOC 1, SOC 2, and ISO 27001. Additionally, BeyondOTC connects clients to custodians offering up to $250 million in crime insurance to protect against fraud, hacking, or key loss. The platform also partners with technology providers that use advanced security protocols to improve custody reporting accuracy. These carefully vetted connections ensure operational security and compliance, reinforcing the integrity of custody reporting.
Conclusion and Key Takeaways
Summary of Best Practices
Institutional custody reporting demands a combination of technical security, legal safeguards, and operational precision. Key steps include keeping client funds separate, ensuring independent certifications validate controls, and using real-time reporting tools for constant audit readiness.
Institutions must confirm that custodians utilize qualified custodian structures, such as regulated banks or trust companies. These structures ensure assets are held in a bankruptcy-remote manner and are backed by robust insurance policies. Considering that cryptocurrency losses reported to the FBI in 2024 surpassed $6.5 billion, these measures are no longer optional – they are critical for safeguarding institutional investments. By adopting these practices, institutions not only reduce risk but also turn custody reporting into a strategic advantage.
Final Thoughts on Custody Reporting
Custody reporting has become a cornerstone for institutional trust and operational resilience. It does more than secure assets; it establishes a foundation of trust and regulatory compliance. For instance, a 2022 BNY Mellon survey revealed that 91% of institutional investors were interested in tokenized assets, underscoring the growing momentum behind digital assets. Institutions that treat custody reporting as an integral part of risk management – not just a compliance requirement – are better equipped to thrive.
"Custody isn’t just about holding assets – it’s about creating a secure, compliant framework for accessing, managing, and moving them."
– ChainUp
With regulations tightening – such as the updated NYDFS guidance in September 2025 that mandates written acknowledgment of custody terms and thorough sub-custodian reviews – institutions that embrace these practices will be well-prepared to navigate the evolving digital asset landscape and achieve long-term growth.
FAQs
What should a custody report prove to me?
A custody report serves as proof that your digital assets are being stored securely and managed responsibly. It should confirm the use of top-tier security practices, such as multi-signature wallets and hardware security modules. Additionally, it should demonstrate compliance with recognized standards like SOC 2 or ISO 27001.
Beyond security, the report should offer clear insights into transaction history, audit trails, and risk management practices. These details ensure your assets are safeguarded from theft, loss, or hacking, providing peace of mind about their protection.
How can I verify my assets are truly segregated?
To ensure your assets are kept separate, look for custody controls such as dual control procedures, precise record-keeping that demonstrates segregation, and adherence to regulatory custody standards. For instance, rules like CASS 6 mandate the proper separation and safeguarding of client assets. Verifying these safeguards can provide confidence in the security and separation of your assets.
What makes a custodian “qualified” in the U.S.?
In the U.S., a custodian is considered "qualified" when it adheres to regulatory standards and prioritizes the secure management of digital assets. To meet these criteria, the entity must be registered or regulated and implement safeguards such as secure storage systems, multi-signature wallets, and hardware security modules. Additionally, regular security audits are essential to ensure ongoing protection. These practices not only align with changing regulations but also help safeguard client assets effectively.




