85% of companies transfer data internationally, but only 34% document their legal processes. This leaves businesses exposed to major risks, including massive fines like Meta‘s €1.2 billion penalty in 2023. Navigating global data laws – like GDPR, China’s PIPL, and the U.S. Data Privacy Framework (DPF) – is complex but critical to avoid financial and operational consequences.
Here’s what you need to know:
- Key regulations: GDPR requires “adequate protection” for EU data. China’s PIPL enforces strict localization. The U.S. DPF allows certified companies to transfer EU data.
- Compliance essentials: Map your data flows, classify data by sensitivity, and use legal tools like Standard Contractual Clauses (SCCs) or Binding Corporate Rules (BCRs).
- Security measures: Encrypt data (TLS 1.3 for transit, AES-256 for storage), implement strong access controls, and ensure regional key management.
- Governance and monitoring: Build a compliance team, update Transfer Impact Assessments (TIAs) regularly, and audit systems to stay current with evolving laws.
Takeaway: Document your data transfers, adopt regional storage models, and use automated tools to simplify compliance. Failing to prepare could cost you millions in fines and damage customer trust.
Cross-Border Data Transfers in 2025: Regulatory Changes, AI Risks, and Operationalization
Cross-Border Data Compliance Basics
Global Data Protection Frameworks Comparison: GDPR vs PIPL vs US DPF
What is Cross-Border Data Compliance?
Cross-border data compliance comes into play whenever personal or sensitive data is sent beyond its country of origin. This can happen through various means, like physical device transfers, cloud storage, remote access, or SaaS tools that operate across borders.
The key factor here is the data’s movement across international boundaries. Whether it’s through electronic transmissions, API calls, emails, or remote access, once data crosses a border, compliance rules kick in. Two important concepts to understand are data residency – where the data is physically stored – and data sovereignty, which refers to the laws governing that data.
Grasping how data moves across borders is essential for navigating the patchwork of international regulations.
Major Regulations for International Data Transfers
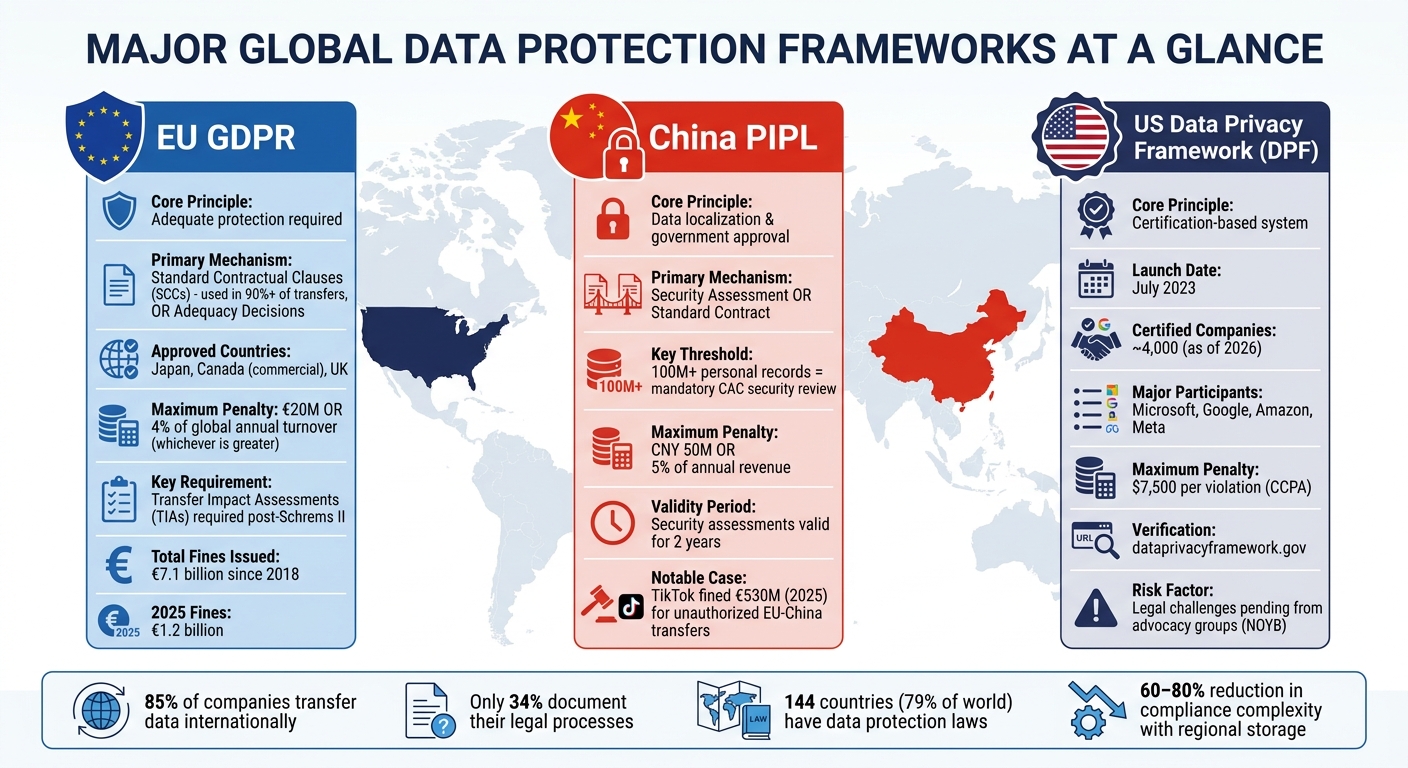
When it comes to global data transfers, three regulatory frameworks dominate the scene:
- The EU’s GDPR: The General Data Protection Regulation requires that data leaving the European Economic Area (EEA) is given "adequate protection." Tools like Standard Contractual Clauses (SCCs) and Adequacy Decisions enable data sharing with approved countries such as Japan, Canada (for commercial sectors), and the UK.
- China’s PIPL: The Personal Information Protection Law emphasizes keeping data within China and requires government oversight for overseas transfers. Businesses handling 100 million or more personal data records must pass a mandatory security review by the Cyberspace Administration of China.
- The Data Privacy Framework (DPF): Introduced in July 2023, this framework offers a certification-based system for EU-to-US data transfers. By 2026, about 4,000 US companies, including Microsoft, Google, Amazon, and Meta, had achieved DPF certification.
As of 2026, 144 countries – representing 79% of the world – have enacted data protection laws, creating a maze of overlapping rules. The 2020 Schrems II ruling added another layer of complexity by requiring Transfer Impact Assessments (TIAs) to ensure that destination-country laws don’t undermine contractual safeguards.
Here’s a quick comparison of these frameworks:
| Jurisdiction | Core Principle | Primary Mechanism | Max Penalty |
|---|---|---|---|
| EU (GDPR) | Adequate protection | SCCs (used in over 90% of transfers) or Adequacy Decisions | €20M or 4% of global turnover |
| US (DPF/State) | Certification-based | DPF or state-specific laws | $7,500 per violation (CCPA) |
| China (PIPL) | Localization & Approval | Security Assessment or Standard Contract | 5% of annual revenue |
These frameworks highlight the high stakes involved, especially as businesses face potential financial and operational fallout from non-compliance.
Consequences of Non-Compliance
Failing to comply with these regulations can be costly. Under GDPR, fines can reach as high as €20 million or 4% of a company’s global annual revenue, whichever is greater. Similarly, China’s PIPL can impose penalties of up to 5% of an organization’s annual turnover. Since GDPR enforcement began in 2018, total fines have surpassed €7.1 billion, with €1.2 billion issued in 2025 alone. Notably, over €3.8 billion – more than 60% of the total – was levied after January 2023.
For example, in 2025, TikTok faced a €530 million fine from Ireland’s Data Protection Commission for transferring personal data of European users to servers in China, contradicting earlier assurances that the data wasn’t stored there.
Beyond monetary penalties, non-compliance can wreak havoc on business operations. Courts can halt data transfers, which can be devastating for companies relying on centralized cloud storage or global SaaS platforms. In 2025, daily breach notifications exceeded 400 for the first time, and the resulting reputational damage can permanently impact customer trust.
Mapping and Managing Your Data Flows
How to Map Data Flows
Before you can tackle cross-border data regulations, you need a clear picture of where your data is going. A cross-border transfer happens whenever data moves between legal jurisdictions. This could mean transferring data via network transmission, storing it in the cloud, or even accessing it remotely. Routing data through a foreign server? That counts too.
Start by building a detailed inventory of all personal data. Break it into categories like Basic, Sensitive, Financial, and HR data. Assign sensitivity levels and note the regulations that apply, such as GDPR Articles 44–49 or PIPL Article 38. Don’t stop at the obvious destinations – map out the entire path, including intermediary stops like edge nodes and subprocessors.
Here’s a reality check: while 85% of global businesses transfer personal data across borders, only 34% have documented how they do it. Your inventory should include the purpose of each transfer, the legal basis, the transfer mechanism (e.g., SCCs, BCRs, or DPF), and any extra security measures in place. If you’re operating in China, check if your data volumes meet thresholds requiring mandatory security assessments – like processing 100 million personal data records or 100,000 sensitive records.
Remote access is another area to watch. If employees or partners access data from outside its region of origin, that’s a transfer too. Make sure you account for every remote access point to stay compliant.
Once your data flows are mapped, the next step is classifying data by its sensitivity to determine the right compliance measures.
Classifying Data by Sensitivity
Not all data carries the same level of risk, so proper classification is key. A tiered system – commonly Standard, Medium, and High/Sensitive – helps organizations decide which transfer mechanisms to use. For example:
- Standard tier: Basic personal data like names, emails, and addresses. Typically handled with standard contractual clauses under frameworks like GDPR or PIPL.
- Medium tier: Financial data, such as transaction records or credit scores.
- High/Sensitive tier: Data like health records, biometric details, or genomic information, which require the strictest safeguards.
Volume also plays a role. Data that might seem low-risk in small amounts can become restricted if processed in bulk.
The U.S. Department of Justice identifies six sensitive data categories: personal identifiers, precise geolocation, biometric data, human ‘omic data (like genomic or proteomic), personal health data, and financial data. For instance, geolocation data from government geofenced areas is always treated as high-sensitivity, regardless of volume.
"Regional data architecture – storing China-originated data in China, EU data in EU regions, and US data in US-certified facilities – reduces cross-border compliance complexity by 60-80% compared to centralized global storage strategies."
– AgentScout
Using Technology for Data Mapping
Managing mapped data and sensitivity classifications efficiently requires modern tools. Manual data mapping simply doesn’t scale. Platforms like OneTrust, BigID, and Transcend automate tasks such as managing standard contractual clauses, conducting transfer impact assessments, and keeping data inventories current. These tools can cut analysts’ preparation workloads from 80% to about 20–30%. Advanced platforms even use AI for semantic matching, reducing setup time for common data sources by up to 70%.
For businesses juggling multiple systems, data integration and ETL tools like Integrate.io, Talend, Informatica, and Dell Boomi unify disparate data fields into cohesive schemas. This makes tracking data across global systems much simpler. No-code tools now cover about 80% of data mapping needs, empowering non-technical staff to manage data flows with ease.
Look for tools with built-in observability features, such as schema drift detection, job failure alerts, and data freshness monitoring. These features ensure compliance stays intact even as technical setups evolve. For example, when the Leukaemia Foundation of Australia implemented Integrate.io, they slashed their data pipeline setup time from two weeks to just 30 minutes. The result? Real-time analytics and a 90% boost in operational efficiency.
Before choosing a tool, confirm that it can track not just the final destination but also intermediary nodes and subprocessors. For U.S. transfers, check that the tool can verify DPF certification using the official list at dataprivacyframework.gov.
Legal Mechanisms for Cross-Border Data Transfers
Standard Contractual Clauses (SCCs) and Binding Corporate Rules (BCRs)
When transferring data internationally, it’s crucial to establish a solid legal foundation. Standard Contractual Clauses (SCCs) are pre-approved agreements that bind both the data exporter and importer to specific data protection responsibilities. These clauses are the go-to solution for transfers to countries that lack an adequacy decision from the European Commission. In fact, SCCs account for over 90% of all international data transfers.
Binding Corporate Rules (BCRs), meanwhile, are internal policies designed for multinational corporations to manage data transfers within their own branches across the globe. Unlike SCCs, BCRs require approval from data protection authorities and are ideal for large organizations with intricate data flows spanning multiple jurisdictions. These rules align well with broader compliance strategies for cross-border data management.
However, using SCCs comes with an additional requirement: each one must be paired with a Transfer Impact Assessment (TIA). This assessment ensures that the laws in the destination country do not undermine the protections outlined in the SCC. Skipping this step can lead to serious compliance issues. For instance, in 2023, Meta Ireland faced a €120 million fine for continuing data transfers to the U.S. using invalidated mechanisms.
While SCCs and BCRs are key safeguards, other mechanisms, like adequacy decisions, also play an important role.
Adequacy Decisions and Alternative Transfer Mechanisms
Adequacy decisions simplify international data transfers significantly. When the European Commission deems a country’s data protection laws to be "essentially equivalent" to EU standards, data can flow freely to that country without additional safeguards.
One recent example is the EU-U.S. Data Privacy Framework (DPF), introduced in July 2023. This framework serves as a specialized adequacy decision for the United States. Around 4,000 U.S. companies – including major players like Microsoft, Google, Amazon, and Meta – have obtained DPF certification. These certified entities can receive EU personal data without requiring SCCs, as long as they self-certify with the U.S. Department of Commerce. To use the DPF, always verify the recipient’s certification status at dataprivacyframework.gov.
"The DPF itself carries political risk. Advocacy organizations, including NOYB (None of Your Business), have publicly stated intent to challenge the DPF in EU courts."
- National Privacy Authority
Given the potential for legal challenges, businesses are encouraged to keep SCCs as a backup option to avoid disruptions if the framework is overturned.
For occasional or one-off transfers, derogations under Article 49 of the GDPR provide exceptions. These include explicit user consent or transfers necessary for contract performance. However, these options are not suitable for routine or large-scale data flows.
Conducting Transfer Impact Assessments (TIAs)
To complement contractual and adequacy safeguards, a Transfer Impact Assessment (TIA) is essential. This evaluation ensures that the legal environment in the recipient country does not compromise the protections in place. The need for TIAs stems from the Schrems II ruling by the CJEU, which invalidated the Privacy Shield and highlighted that contractual safeguards alone are insufficient if local laws allow excessive government surveillance.
A thorough TIA examines several factors, including surveillance laws in the destination country (e.g., FISA 702 in the U.S.), the presence of independent oversight, and the availability of legal remedies for data subjects. If risks are identified, additional measures – such as end-to-end encryption with no access to decryption keys by the importer – must be implemented to ensure an "essentially equivalent" level of protection.
Here’s a simple four-step approach to conducting a TIA:
- Research the legal environment in the destination country.
- Document the specifics of your data transfer scenario.
- Identify and implement any necessary supplementary safeguards.
- Evaluate and document any residual risks.
It’s also critical to assess the entire chain of subprocessors. If your vendor relies on third-party services in other non-adequate countries, those onward transfers must also be evaluated.
For companies operating in China, the stakes are even higher. Under the Personal Information Protection Law (PIPL), processing 100 million or more records triggers a mandatory security assessment by the Cyberspace Administration of China (CAC). This is not a self-assessment – it requires government approval and is valid for two years.
Many businesses overlook updating their TIAs when adding new subprocessors, which can break the liability chain and make onward transfers unlawful. Treat TIAs as dynamic documents that require regular updates – ideally reviewed annually. This is especially important given the evolving landscape of surveillance laws and political factors. Regular updates ensure compliance and help mitigate risks tied to international data transfers.
sbb-itb-7e716c2
Technical Security Measures for Data Protection
Encryption Standards for Data in Transit and At Rest
Protecting data both in transit and at rest requires robust encryption protocols. For securing data during transmission, TLS 1.3 is the go-to protocol. It prevents interception attacks and ensures data confidentiality as it moves across global networks. Upgrading to TLS 1.3 typically costs between $5,000 and $50,000.
When it comes to stored data – whether on servers, in the cloud, or on user devices – AES-256 is the most widely used encryption standard. Implementing AES-256 storage systems can cost anywhere from $10,000 to $100,000. While ISO 27001 leaves room for flexibility in algorithm selection, frameworks like CMMC demand the use of FIPS-validated cryptography to meet compliance requirements.
A high-profile case in April 2023 highlighted the importance of these safeguards. Meta Platforms Ireland faced a €1.2 billion fine from the Irish Data Protection Commission for transferring Facebook user data to the U.S. using SCCs without sufficient technical measures to protect against U.S. surveillance. This incident illustrates that encryption alone isn’t enough – it must be implemented effectively to block unauthorized access, even by the data importer.
Encryption is the foundation, but it needs strong access controls and key management to remain effective.
Access Controls and Key Management
Encryption is only as secure as the system managing the keys. Unauthorized access to decryption keys can render even the most advanced encryption useless. Role-Based Access Control (RBAC) ensures that access to sensitive data is limited to authorized personnel. More advanced systems, like Attribute-Based Access Control (ABAC), add contextual factors such as user location, device compliance, and time of access, helping to enforce sovereignty rules.
To bolster access security, configure your Identity and Access Management (IAM) system with geo-fencing. This feature blocks access based on location, preventing accidental or malicious cross-border data transfers. Deploying an IAM system typically costs between $10,000 and $50,000.
Encryption keys should always be stored within the same region as the data they protect. Cloud-native tools such as AWS KMS, Azure Key Vault, and Google Cloud KMS offer region-specific key management solutions. For added protection, Hardware Security Modules (HSMs) can securely store encryption keys in dedicated hardware. Regular, automated key rotation is also essential to reduce the risk of human error. Keeping data within its region of origin can simplify compliance efforts by as much as 60–80%.
Vendor Contract Security Requirements
Technical safeguards are only part of the equation. When working with third-party vendors, contracts must explicitly outline security requirements. The 2021 Modular SCCs (Modules 2 and 3) are essential for defining these standards, as older SCC versions from 2010 are no longer valid.
Contracts should detail technical measures in their annexes, such as requiring TLS 1.3 for data in transit and AES-256 for stored data. Before relying on the EU–U.S. Data Privacy Framework (DPF), verify a vendor’s certification status at dataprivacyframework.gov. As of 2026, around 4,000 U.S. companies, including Microsoft, Google, Amazon, and Meta, have obtained DPF certification. For vendors without certification, SCCs paired with supplementary measures are mandatory.
| Security Measure | Contractual Specification | Implementation Standard |
|---|---|---|
| Encryption in Transit | Mandatory for all cross-border flows | TLS 1.3 or higher |
| Encryption at Rest | Required for all stored sensitive data | AES-256 |
| Pseudonymization | Tokenization for sensitive fields | Irreversible or high-entropy tokens |
| Access Controls | Role-Based Access Control (RBAC) | Least privilege principle |
| Audit Logging | Comprehensive transfer and access logs | Immutable, time-stamped records |
Other important contract provisions include requiring vendors to assist with Transfer Impact Assessments (TIAs) and promptly notify you of any government data access requests. Additionally, contracts should include "cascading liability" clauses. This ensures that if a vendor in a high-risk jurisdiction fails to meet security standards, you remain legally accountable for regulatory investigations and potential lawsuits.
Building a Governance Framework for Compliance
Creating a Cross-Border Data Compliance Team
After implementing legal and technical safeguards, the next step is ensuring they are managed effectively through a well-structured governance framework. For this, assembling the right compliance team is critical. Ideally, this team should include four key layers:
- Data Governance Committee: Provides strategic oversight.
- Data Owners: Senior-level leaders who define policies.
- Data Stewards: Handle day-to-day management.
- Data Custodians: Focus on implementing technical security measures.
Each role should have clearly defined decision-making authority. To mitigate the risks of non-compliance, it’s essential to allocate responsibilities for managing data flows efficiently. A governance charter should outline escalation paths, policy approval processes, and roles during audits or breaches. Senior management must endorse compliance programs and assign domain-level owners (e.g., Finance, HR) who are accountable for data management in their areas.
The impact of a formal governance framework is quantifiable. For example, 66% of organizations report better data security, while 52% experience fewer compliance breaches after implementing such measures. Moreover, poor data quality can cost businesses an average of $12.9 million annually.
| Role | Primary Responsibility | Key Deliverable |
|---|---|---|
| Data Governance Committee | Strategy and policy definition | Governance Framework & Charter |
| Data Owners | Strategic decisions and policy approval | Data Policy & Security Standards |
| Data Stewards | Daily management and quality checks | Data Accuracy & Compliance Reports |
| Data Custodians | Technical storage and infrastructure | Secure Backups & Encryption |
| Legal Counsel | Jurisdiction and conflict analysis | Transfer Impact Assessments (TIAs) |
With a strong team in place, well-defined policies and procedures become the backbone of long-term compliance.
Developing Policies and Procedures
A solid compliance strategy starts with detailed policies that classify data based on sensitivity and document all cross-border data flows. This includes mapping primary destinations, intermediary nodes, and subprocessor chains. Such an inventory forms the foundation for compliance efforts, supporting both legal and technical safeguards.
Policies should also incorporate Transfer Impact Assessments (TIAs) and regular vendor risk evaluations. Notably, around 4,000 U.S. companies, including Microsoft, Google, Amazon, and Meta, have obtained DPF certification. Automating policy enforcement with metadata-driven systems can streamline compliance processes.
Continuous Monitoring and Auditing
Even with strong policies in place, ongoing monitoring and regular audits are essential to keep compliance measures effective and up to date. A centralized compliance dashboard can track vital details like active Standard Contractual Clauses (SCC) contracts, DPF certifications, and TIA review dates.
| Activity | Frequency | Responsible Party |
|---|---|---|
| DPF Certification Check | Monthly | IT Security |
| Transfer Mechanism Validity | Quarterly | DPO / Compliance Team |
| Access Control Reviews | Quarterly | Data Custodians |
| TIA Review & Update | Annually | Legal Counsel |
| Independent Compliance Audit | Annually | Compliance Team |
Quarterly reviews should involve Data Owners and Stewards reporting on data health metrics and the effectiveness of transfer mechanisms. Accountability should be embedded into job descriptions and performance goals. Additionally, creating a shared communication channel – like a Slack workspace or dedicated portal – can help streamline issue reporting and policy suggestions.
The stakes for non-compliance are substantial. For instance, cumulative GDPR fines have surpassed €5.88 billion, with €1.2 billion issued in 2024 alone. Similarly, under China’s PIPL, fines can reach up to CNY 50 million or 5% of global annual turnover. Regular monitoring ensures potential issues are caught early, reducing the risk of costly regulatory penalties.
Conclusion
Cross-border data compliance demands constant vigilance and effort. Successful organizations embed a privacy-by-design mindset from the very beginning, weaving compliance into their processes rather than scrambling to fix gaps later.
As highlighted earlier, while international data transfers are common, few businesses fully document their mechanisms – leaving them vulnerable. This risk is underscored by €5.88 billion in cumulative GDPR fines, including Meta Ireland’s staggering €1.2 billion penalty. The Meta case serves as a cautionary tale, illustrating the consequences of unauthorized EU–US data transfers without proper safeguards.
To achieve sustainable compliance, focus on three key pillars: proactive planning, technology integration, and strong governance. Start by mapping all data flows and, when possible, adopt regional data storage solutions. This approach can cut compliance complexity by as much as 60–80%. Leverage automated tools for real-time visibility into data transfers, as manual processes often overlook unintentional transfers through cloud edge nodes or subprocessors. These technical measures lay the groundwork for a broader governance strategy.
Your governance framework should encourage collaboration across departments – legal, IT, marketing, and operations must work together. Alex Spokoiny, Chief Information Officer at Check Point Software Technologies, emphasizes:
"Privacy compliance can become a competitive advantage when approached proactively".
Stay ahead by keeping Transfer Impact Assessments dynamic, updating them as legal requirements evolve, rather than treating them as a one-time task.
With deadlines like the EU AI Act’s full enforcement on August 2, 2026, fast approaching, businesses that prioritize visibility, automation, and collaboration can turn compliance from a challenge into a genuine advantage.
FAQs
What counts as a cross-border data transfer (including remote access)?
A cross-border data transfer happens when personal data is moved between different jurisdictions. This can occur through various means – network transmission, cloud storage, remote access, or even physical media. For example, accessing data stored in one country from another, such as via remote login or cloud access, is considered a transfer. Even if the data stays physically in its original country, remote access from another location counts as a transfer and could bring compliance requirements under regulations like GDPR or PIPL.
How do I choose between SCCs, BCRs, and the EU–U.S. Data Privacy Framework?
Choosing the right data transfer mechanism – Standard Contractual Clauses (SCCs), Binding Corporate Rules (BCRs), or the EU–U.S. Data Privacy Framework (DPF) – depends largely on your organization’s structure, compliance requirements, and the jurisdictions involved.
- SCCs: These offer flexibility and are commonly used for transferring data to countries outside the EU that don’t have an adequacy decision. They’re particularly useful for businesses working with third-party vendors or partners in such regions.
- BCRs: Designed for large multinational companies, BCRs provide a reliable way to manage internal data transfers across global offices while ensuring compliance with EU data protection standards.
- DPF: If your organization meets the certification criteria, the DPF simplifies data transfers between the EU and the U.S., reducing the complexity of compliance for transatlantic operations.
Each option serves a specific purpose, so the choice should align with your operational needs and regulatory obligations.
When do I need a Transfer Impact Assessment (TIA), and how often should it be updated?
A Transfer Impact Assessment (TIA) is essential for evaluating the risks involved in cross-border data transfers. Its primary goal is to assess how foreign laws or surveillance practices might impact the privacy and security of the data being transferred.
It’s important to update TIAs whenever there are major changes, such as entering new jurisdictions, updates in legal frameworks, or modifications in data processing activities. Additionally, conducting regular reviews helps maintain compliance and adapt to any new risks that may arise over time.