Managing digital assets securely is a top priority for institutions. Institutional crypto custody revolves around safeguarding private keys, which control access to digital assets. With over $6.5 billion in crypto losses reported in 2024, the need for secure custody solutions is clear.
Key takeaways:
- Security: Custodians use advanced methods like Multi-Party Computation (MPC), air-gapped cold storage, and Hardware Security Modules (HSMs).
- Compliance: Providers must meet strict regulatory standards, including OCC charters, NYDFS licenses, and asset segregation rules.
- Custody Models: Options include self-custody, third-party custody, or hybrid models. Each has trade-offs in control, risk, and cost.
- Evaluation: Institutions should assess security protocols, insurance coverage, licensing, and independent audits before choosing a provider.
The collapse of Prime Trust in 2023 (losing $82 million) highlights the risks of poor custody practices. On the other hand, firms like BNY Mellon and BitGo showcase effective custody strategies with robust security and compliance measures. Whether you’re managing long-term holdings or frequent transactions, selecting the right custody solution is critical for safeguarding assets.
Core Features of Institutional Crypto Custody
Security Infrastructure
Protecting digital assets in institutional custody requires a multi-layered security approach. At the heart of this is offline, air-gapped cold storage, which safeguards assets from network-based attacks. Most custodians store the majority of their holdings in these offline environments, minimizing exposure to potential online threats.
Multi-Party Computation (MPC) has emerged as a key solution for secure key management. Instead of storing a complete private key in one location, MPC divides it into encrypted fragments distributed among multiple parties. This ensures the full key is never assembled in a single place, effectively removing the risk of a single point of failure seen in older methods. To further enhance security, Hardware Security Modules (HSMs) – tamper-resistant devices certified to FIPS 140-2 Level 3 or higher – are used to generate and store these key fragments securely offline. Any attempt to tamper with these modules leaves an auditable trail or triggers automatic key destruction.
Additional safeguards include multi-signature wallets, which require multiple independent approvals (e.g., 3-of-5 signatures) for transactions. Operational controls such as address whitelisting, withdrawal limits, and mandatory human reviews for large transfers add further layers of protection. Geographic redundancy is another critical measure; key fragments or backups are stored across different physical locations to guard against regional disasters or localized theft. While these advanced security protocols are vital, they must operate in tandem with strict regulatory compliance.
Compliance Requirements
Once a secure infrastructure is established, custodians must navigate rigorous regulatory standards. In the U.S., this begins with proper licensing. Custodians need either a federal charter from the Office of the Comptroller of the Currency (OCC) or a state-level trust license, such as those issued by the New York Department of Financial Services (NYDFS). A milestone in regulatory acceptance occurred when Anchorage Digital Bank became the first crypto-native institution to secure an OCC federal charter, setting a standard for others to follow. For those serving registered investment advisers or hedge funds, custodians must meet "qualified custodian" requirements under the Investment Advisers Act of 1940.
An essential compliance element is asset segregation, which ensures client assets are held in distinct trust accounts, separate from the custodian’s operational funds. This protects client holdings in the event of insolvency. Broker-dealers face additional obligations under SEC Rule 15c3-3, which requires "physical possession" or control of fully paid digital asset securities. To combat illicit activities, custodians implement Anti-Money Laundering (AML) and Know Your Customer (KYC) measures. Many also utilize Know Your Transaction (KYT) tools like Chainalysis or Elliptic for monitoring on-chain activity. Insurance coverage is another layer of protection; for example, BitGo offers up to $250 million in coverage for losses due to theft or misuse when they hold all keys. These measures, combined with strong governance, ensure operational integrity.
Governance and Reporting Standards
Strong governance protocols are critical for safeguarding institutional assets and minimizing risks. Measures such as multi-approver workflows and role-based access controls reduce the chances of insider threats or operational mistakes. The "four-eyes principle", which requires at least two authorized individuals to approve transactions, is widely adopted. Institutions can further tailor approval policies based on transaction size or asset type to align with their internal risk management strategies.
To demonstrate operational reliability, many custodians seek SOC 2 Type 2 certification, which verifies that security controls are effective over time – typically over a 6 to 12-month period – rather than just at a single point. These certifications provide the transparency needed to meet fiduciary obligations and satisfy regulatory scrutiny. Additionally, real-time reporting and API-driven workflows allow for automated reconciliation with treasury and order management systems, reducing manual errors while maintaining 24/7 oversight. For example, Anchorage Digital processes 90% of transactions in under 20 minutes, all while adhering to compliance standards.
sbb-itb-7e716c2
The Truth About Institutional Crypto Custody – Are Your Assets REALLY Safe?
Custody Models for Institutions
Institutional Crypto Custody Models Comparison: Self-Custody vs Third-Party vs Hybrid
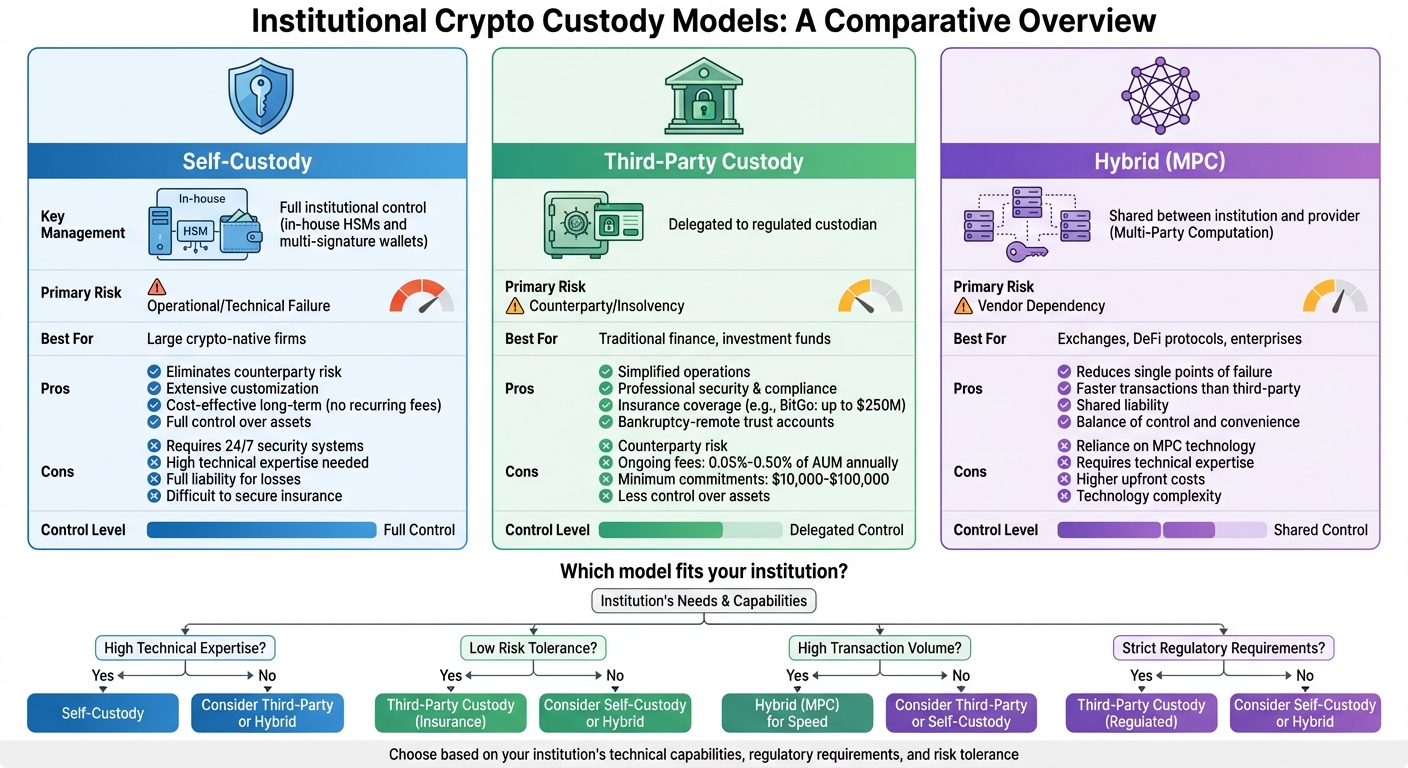
Institutions have three main ways to handle digital assets, each balancing control, security, and operational demands. The right choice depends on factors like technical expertise, regulatory obligations, and risk tolerance.
Self-Custody
With self-custody, institutions take full responsibility for managing private keys using in-house hardware security modules (HSMs) and multi-signature wallets. This approach eliminates counterparty risk, allows for extensive customization, and can be cost-effective over time – particularly for crypto-focused firms with dedicated blockchain teams. By avoiding recurring custody fees, it’s a popular choice for those with the necessary resources.
However, self-custody isn’t without challenges. Institutions must maintain robust, 24/7 security systems, handle cryptographic keys independently, and bear full liability for potential losses. Securing insurance can be difficult, and the technical demands require specialized knowledge, which can be a major hurdle for traditional financial firms.
Third-Party Custody
Third-party custody shifts key management responsibilities to regulated providers. For example, major banks are now offering digital asset platforms, and in October 2021, U.S. Bank became one of the first major retail banks to provide cryptocurrency custody services for institutional clients.
This model is attractive for traditional financial institutions and investment funds because it simplifies operations. Custodians handle security and compliance and often provide insurance – BitGo, for instance, offers coverage up to $250 million for losses due to theft or misuse. Additionally, assets are held in bankruptcy-remote trust accounts, adding an extra layer of protection. The downside? Institutions face counterparty risk and ongoing fees, which typically range from 0.05% to 0.50% of assets under management annually, with minimum commitments between $10,000 and $100,000. The decision ultimately comes down to balancing convenience with risk.
Hybrid Custody Models
Hybrid models blend self-custody and third-party custody by leveraging Multi-Party Computation (MPC). This technology splits private keys into encrypted fragments shared between the institution and the provider. Since the full key is never assembled in one place, this setup reduces single points of failure while maintaining security and accessibility. It’s particularly useful for exchanges and DeFi protocols that require high transaction throughput alongside strong security.
This shared-control approach spreads liability and allows for quicker transactions compared to traditional third-party models. However, it introduces reliance on MPC technology and requires technical expertise to implement effectively. While upfront costs may be higher, hybrid models offer flexibility that can be appealing for institutions needing a balance between control and convenience.
| Custody Model | Key Management | Primary Risk | Best For |
|---|---|---|---|
| Self-Custody | Full institutional control | Operational/Technical Failure | Large crypto-native firms |
| Third-Party | Delegated to custodian | Counterparty/Insolvency | Traditional finance, investment funds |
| Hybrid (MPC) | Shared between parties | Vendor Dependency | Exchanges, DeFi protocols, enterprises |
Choosing the right custody model or provider is critical, as each option comes with its own set of benefits and trade-offs.
How to Evaluate Custody Providers
Choosing the right custody provider is no small task. A structured due diligence process is essential, with a focus on security, licensing, and audits. With cryptocurrency losses reported to the FBI reaching over $6.5 billion in 2024 alone, institutions must be thorough when vetting potential partners. The collapse of Prime Trust in June 2023 is a cautionary tale – a staggering $82 million shortfall emerged due to operational failures and the commingling of funds, leaving clients exposed. Here’s what institutions need to examine before entrusting their assets to any custodian.
Security and Operations
Security measures are the backbone of any custody provider. It’s critical to confirm that the provider employs industry-standard practices, such as Multi-Party Computation (MPC) and FIPS 140-2 Level 3 certified Hardware Security Modules (HSMs).
Storage practices are another key area to investigate. Top custodians typically keep 90% to 95% of assets in offline cold storage, with only the necessary liquidity in online wallets for operational needs. Ensure you ask for specifics on how assets are allocated between cold and hot storage, as well as how frequently transfers occur.
Operational safeguards like whitelisting, withdrawal limits, and multi-person approval for large transactions are equally important. Test these workflows in a sandbox environment to ensure smooth API integration with your existing systems.
Insurance coverage is another layer of protection. For example, BitGo offers up to $250 million in coverage for the digital assets it secures with its keys. Make sure the policy covers both hot and cold storage and includes protection against theft, internal collusion, and key loss.
Geographic redundancy and disaster recovery protocols are non-negotiable. Providers should maintain distributed backups and have a tested disaster recovery plan with a clear Recovery Time Objective (RTO). Ask for documentation from recent disaster recovery drills to confirm these practices. Together, these measures create a robust framework to safeguard your assets.
Licensing and Regulatory Status
Regulatory compliance is a critical factor when selecting a custody provider. In the U.S., check if the provider holds a bank charter from the Office of the Comptroller of the Currency (OCC), a NYDFS State Trust license, or qualifies as a "Qualified Custodian" under SEC rules. Anchorage Digital, for instance, became the first crypto-native company to receive a federal bank charter from the OCC in January 2021, proving that crypto firms can meet traditional banking standards.
For institutions operating in the EU, confirm the provider has MiCA authorization, which became fully applicable in December 2024, to meet harmonized licensing standards across member states. The 2025 repeal of the SEC Staff Accounting Bulletin 121 has also removed significant accounting hurdles, allowing more traditional banks to offer custody services. Even with regulatory advancements, it’s essential to verify the specific licensing status of each provider in your jurisdiction. Proper regulatory credentials reduce counterparty risk, ensuring that security and compliance go hand in hand.
Once regulatory credentials are confirmed, independent audits should be reviewed to verify ongoing operational integrity.
Audits and Certifications
Independent audits and certifications are vital for evaluating a custody provider’s reliability. SOC 2 Type 2 reports are widely regarded as the benchmark for demonstrating operational security over an extended period (typically 6 to 12 months). Request full reports and review any control exceptions. SOC 1 Type 2 reports, which focus on financial reporting controls, provide additional assurance.
Certifications like ISO 27001 validate the provider’s information security management system. Regular penetration tests and vulnerability assessments are also essential, and updated results should be available for review. Providers should conduct periodic cryptographic audits to evaluate the security of their MPC or multi-signature protocols.
Proof of Reserves (PoR) assessments are another critical tool. These assessments confirm that the custodian maintains a 1:1 backing of client assets without commingling funds. Ensure that client assets are held in bankruptcy-remote trust accounts, legally separated from the custodian’s operational funds. The Prime Trust collapse underscored the importance of proper asset segregation, as poor practices contributed to its significant shortfall.
"Even a small share of the $100T+ overseen in traditional finance moving into crypto makes mastery of safe custody essential."
– Haydn Jones, PwC
Ultimately, cutting corners on custody can lead to far greater losses than any potential fee savings.
Implementation and Integration
Once you’ve chosen a custody provider, the next step is navigating the 14- to 26-week implementation process. This journey begins with the Requirements Definition phase, which takes 2 to 4 weeks. During this time, you’ll evaluate your asset types, transaction volumes, and compliance needs. It’s also the stage to define success metrics, such as achieving key security certifications like SOC 2 Type 2 and ISO 27001, and setting minimum insurance coverage levels.
The next step is Vendor Evaluation, lasting 4 to 6 weeks. Shortlist 3 to 5 providers and thoroughly assess their security frameworks, regulatory credentials, and asset segregation policies. To ensure you’re making the right choice, conduct a Proof of Concept (PoC) in a sandbox environment to test critical workflows before committing.
The Technical Integration phase, which spans 6 to 12 weeks, focuses on connecting the custody platform’s APIs to your existing systems, such as trading platforms, treasury tools, and accounting software. You’ll also configure key security features like multi-approver workflows, role-based access controls, and whitelisted withdrawal addresses. For instance, when BNY Mellon launched its digital asset custody platform in October 2022, it partnered with Fireblocks for security and Chainalysis for compliance monitoring. These steps ensure a secure and seamless transition from the evaluation phase to daily operations.
Tailoring the integration process to your specific needs is crucial, so start by assessing your custody requirements.
Assessing Custody Needs
Understanding your asset portfolio and transaction patterns is key. Whether your focus is long-term treasury holdings like Bitcoin and Ether or frequent trading and staking, your custody strategy should align with your operational goals. For example, in 2021, Tesla invested $1.5 billion in Bitcoin for treasury purposes, highlighting the importance of institutional-grade security.
Regulatory compliance is another critical consideration. In the U.S., investment advisers are often required to use "qualified custodians", such as regulated banks or trust companies, to safeguard client assets. If your operations span multiple regions, ensure your provider holds the appropriate licenses. For EU-based institutions, confirm MiCA authorization, which became fully applicable in December 2024.
Storage strategy is another key factor. Leading custodians typically store 90% to 95% of assets in cold storage, with only 1% to 5% in hot wallets for immediate needs. A tiered approach – using cold storage for long-term holdings, warm storage (5% to 10%) for planned transactions, and hot wallets for daily liquidity – offers a balance between security and accessibility.
System Integration
API connectivity is the backbone of a smooth integration. Your custody platform should integrate seamlessly with systems like Order Management Systems (OMS), Portfolio Management Platforms (PMS), and prime brokers. Use sandbox environments provided by your custody provider to test connectivity and handle exceptions before moving to live operations.
Workflows should reflect your internal approval structures. Multi-approver processes and role-based access controls add layers of oversight, ensuring no single individual can authorize large transactions. Whitelisting withdrawal addresses further minimizes the risk of unauthorized transfers.
For institutions working with multiple custody providers, middleware platforms can simplify operations by unifying various solutions under one API. Incorporating tools like Chainalysis or Elliptic directly into your custody workflow can automate compliance by monitoring transactions in real time. Before moving all assets, conduct a pilot migration with small amounts to confirm that reconciliation and reporting processes are functioning as expected.
Monitoring and Maintenance
Ongoing monitoring is essential for maintaining security. Implement 24/7 monitoring and incident response plans to address cyber threats swiftly. Regular asset reconciliation ensures that custodied holdings match internal records, while automated Proof of Reserves reporting verifies 1:1 backing for client assets.
Annual independent security audits are non-negotiable. Review SOC 2 Type 2 reports to evaluate operational controls over time, and conduct regular penetration tests and cryptographic audits to validate the security of protocols like Multi-Party Computation (MPC) or multi-signature systems. Rotating key shares periodically can also help prevent long-term exposure.
Disaster recovery testing is another critical component. Simulate incidents to verify redundant key backups and measure your Recovery Time Objective (RTO). For example, Cobo has maintained a zero-incident security record since 2017 by adhering to SOC 2 Type 2 and ISO 27001 standards and rigorously testing its disaster recovery protocols.
The collapse of Prime Trust underscores the importance of robust monitoring. Operational missteps, such as losing private keys and commingling customer funds, led to an $82 million shortfall and the provider’s eventual downfall. Regular reviews of governance structures, transaction limits, and approval processes can help prevent similar outcomes, ensuring your custody operations remain secure and compliant.
Conclusion
Choosing the right institutional crypto custody solution is a critical decision. Digital assets, being bearer instruments, put full responsibility on the key holder. If keys are lost, the assets are gone forever. With cryptocurrency losses reported to the FBI exceeding $6.5 billion in 2024, the importance of secure custody is undeniable. As Haydn Jones from PwC emphasized:
Even a small share of the $100T+ overseen in traditional finance moving into crypto makes mastery of safe custody essential.
To address these challenges, top-tier custody providers implement safeguards like MPC or multi-signature solutions to avoid single points of failure. They store 90%–95% of assets in cold storage and ensure bankruptcy-remote asset segregation. Compliance is another cornerstone – providers should hold licenses such as an OCC charter, state trust company status, or MiCA authorization. Certifications like SOC 2 Type II and ISO 27001 further validate their operational security. Additionally, insurance policies ranging from $50 million to over $1 billion offer an extra layer of protection.
These measures are essential for maintaining both operational security and regulatory compliance in the ever-changing digital asset landscape. Institutions seeking expert guidance can turn to BeyondOTC. By leveraging a network of trusted custodians, legal advisors, and compliance specialists, BeyondOTC bridges the gap between traditional finance and digital asset custody needs.
The consequences of poor custody choices are stark. The collapse of Prime Trust, which lost private keys and mismanaged funds, resulted in an $82 million shortfall. On the other hand, innovations like BNY Mellon’s 2022 digital asset custody platform highlight the potential for secure and reliable solutions. The decision you make will shape the future of your institution’s digital asset strategy.
FAQs
How do I choose between self-custody, third-party custody, and hybrid MPC custody?
Choosing the right custody model hinges on your organization’s specific security demands, available resources, and compliance obligations.
- Self-custody gives you complete control over your assets but demands a robust and sophisticated security setup.
- Third-party custody provides professional-grade security and support, though it requires placing trust in an external provider.
- Hybrid MPC custody splits key control, offering a balance of security and adaptability.
Carefully assess these choices by considering your risk appetite, operational capabilities, and regulatory requirements.
What licenses and ‘qualified custodian’ requirements should I verify in the U.S.?
In the U.S., make sure the custody provider holds a license as a qualified custodian under applicable regulations. Look into their registration with organizations like the SEC or FINRA to confirm they meet federal and state securities laws. Additionally, ensure they follow proper audit and reporting standards to maintain both security and trustworthiness.
What proof can a custodian provide that my assets are segregated and fully backed?
A custodian shows asset segregation and backing by keeping assets in separate trust accounts, offering verifiable statements that confirm ownership and value, and maintaining both legal and technical control over private keys. Independent audits and adherence to regulatory standards add another layer of transparency, ensuring proper asset management and building trust.